Facebook and Illegal Wildlife Trade
Strategic Investigative Protocol: Disrupting Transnational Illegal Wildlife Trade (IWT) on Social Media Infrastructure
According to the April 2026 Global Initiative Against Transnational Organized Crime report:
1. Operational Context: The Digital Shift in Environmental Exploitation
The global biodiversity crisis has transitioned from a conservation concern to a primary law enforcement priority. We are currently witnessing a "sixth mass extinction"—an episode of human-driven biological decline where direct exploitation remains the most immediate and destructive pathway to species loss. Social media platforms, specifically Facebook, have evolved from peripheral communication tools into the dominant digital infrastructure for this exploitation. For the modern intelligence officer, the digital landscape is no longer a secondary theater; it is the primary environment where global biodiversity is being liquidated.
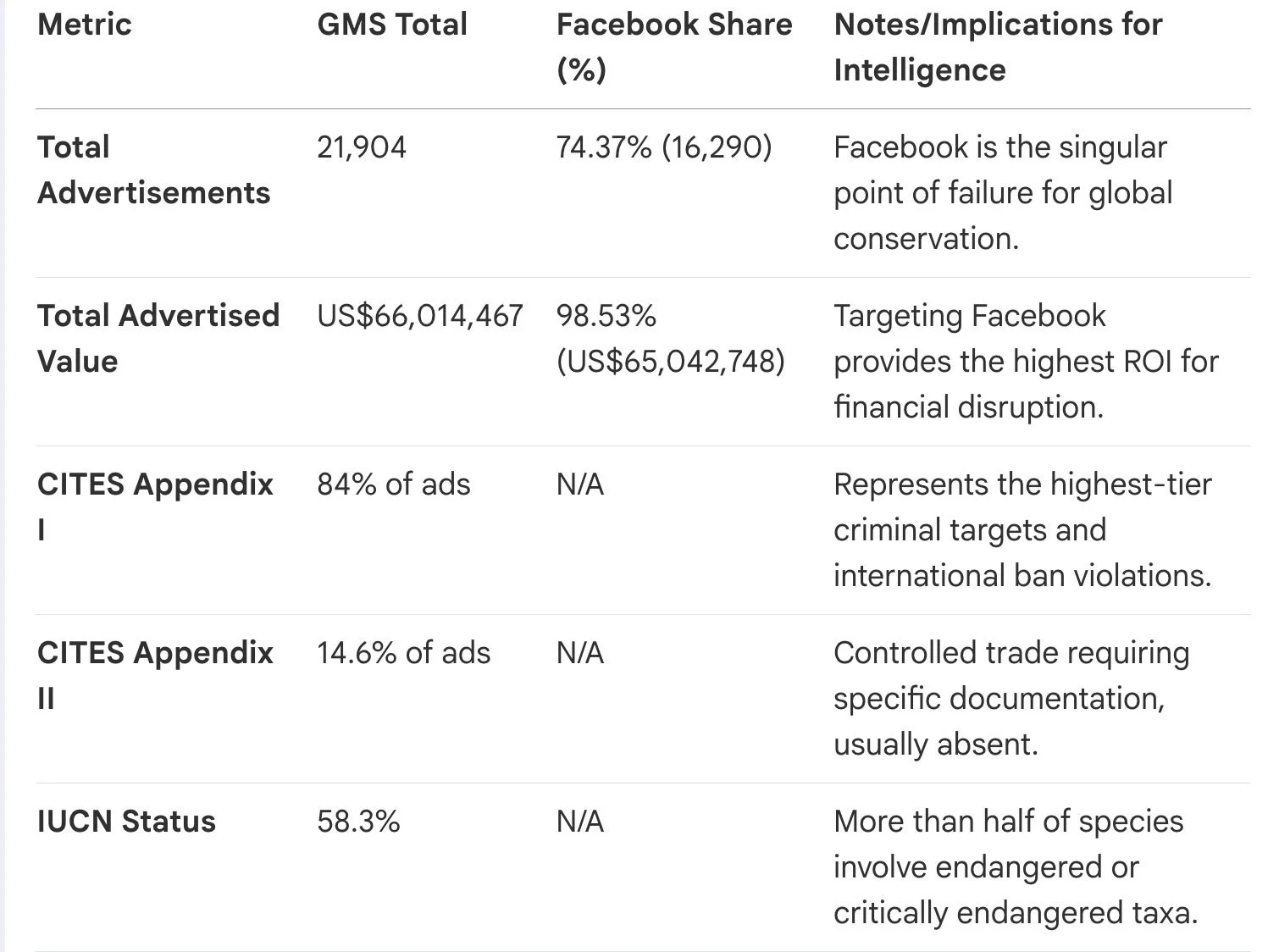
Quantifying the Threat Landscape: Global Monitoring System (GMS) Data
Intelligence analysts must recognize that IWT is not evenly distributed across the web. Data from the GMS (April 2024–March 2026) reveals a near-monopoly by Facebook in the illicit marketplace.
Historical Evolution and OPSEC Analysis
Investigation of IWT must be informed by the evolution of trafficker OPSEC. In the late 1990s, the trade was a "niche" activity for the internet-literate. By 1999, reports in Singapore already noted a 350% increase in seizures linked to traders using pagers and false names to coordinate internet-originated deals. Modern traffickers have traded this fragmentation for the scale of algorithmic discovery.
The Tactical "So What?": The centralization of 74% of ads and 98% of market value on a single platform creates a massive vulnerability for criminal networks. While the algorithm serves as the trafficker’s "marketing department," it also provides a unified data set for law enforcement to exploit. Strategic interventions targeting this platform’s architecture can result in disproportionate disruption across four continents.
2. Deconstructing the Digital Trafficking Lifecycle
The modern illicit wildlife transaction follows a predictable "funnel" from public visibility to private finalization. Analysts must map this lifecycle to identify points of interdiction.
The Discovery-to-Transaction Pipeline: Operational Phases
Phase I: Discovery (Algorithmic Push): 78% of Facebook IWT content is encountered without active searching. Intelligence units should utilize "clean" avatars—profiles with no history—to map how platform algorithms proactively surface illicit content. Data suggests that features like "Related Pages" account for 29% of discoveries, effectively pointing investigators toward criminal clusters.
Phase II: Negotiation (Thematic Groups): Groups are the primary locus, hosting 76% of detections. These function as "Thematic Places" where "Admin curation" serves as a gate for trust. Groups are often aggregated by product themes (e.g., "Pangolins & scales") and utilized for cross-posting to maximize reach.
Phase III: Migration (Dark Communication): Transactions originate in groups but migrate to encrypted messaging (WhatsApp/Messenger) and secondary financial channels (personal bank transfers) to finalize the deal.
Intelligence Directive: Algorithmic Force Multipliers
Investigators shall treat "Suggested Groups" and "Related Pages" as automated mapping tools. By interacting with a single "Seed Account" or group, investigators can trigger the platform to reveal an entire network of related criminal actors. The algorithm essentially performs the preliminary network analysis for the investigator, surfacing 76% of algorithmic suggestions that blatantly seek to trade endangered species.
3. Exploiting Platform Governance Failures for Intelligence
Governance failures—specifically anonymity, monetization contradictions, and language bias—provide critical entry points for investigative mapping.
Target Profile: The Poacher-Influencer
Analysts should prioritize the identification of "Poacher-Influencers" who utilize Meta’s monetization tools to fund illegal activities.
Indicator of Interest: Subscription-enabled pages that monetize exclusive hunting/trafficking content.
The April 2026 GI-TOC report highlights one subscription-enabled page, identified as ‘APC nuj ntxiag ham channel: A single subscription-enabled page grew by 166,000 followers in one month, reaching 195,000 total followers while providing a constant feed of hunting threatened wildlife (clouded leopards, Sunda pangolins, gibbons). The report says the channel grew rapidly while posting content depicting the hunting of threatened wildlife. If those findings are accurate, such accounts could merit closer review by platform moderators and, where appropriate, law enforcement.
Tactical Exploitation of "Language Bias"
A critical investigative gap exists where 88% of IWT advertisements are in non-English languages, yet platform moderation remains "sporadic" in these sectors.
Investigative Requirement: Recruitment and deployment of multilingual OSINT analysts is mandatory. English advertisements account for only 12% of the market. The lack of platform oversight in regional dialects (e.g., Thai, Lao, Indonesian, Spanish) allows traffickers to operate with low fear of reprisal, creating a target-rich environment for law enforcement.
Bypassing Internal Reporting
Voluntary reporting through platform interfaces is an ineffective investigative trigger. In a controlled experiment, a group explicitly named "Pangolins & scales" was reported to Facebook; the platform's "Decision made" was that the group did not violate Community Standards. Analysts shall not rely on platform moderation for disruption; all identified criminal activity must be channeled directly into law enforcement interdiction pathways.
4. Tactical Protocol: FININT and Logistical Collection Requirements
The "back-end" of the transaction—the financial and physical movement—provides the most actionable evidence for international coordination.
FININT Collection Requirements (Target Commodities)
Analysts must document financial artifacts associated with the trade of the following Target Commodities: Bear bile, cobras, pangolin scales, bats, scorpions, slow loris, tigers, and elephant ivory. Specific evidentiary artifacts to seek include:
Proof of Legitimacy: Screenshots of personal bank transfers and transaction receipts posted by sellers to groups to "verify" their status.
Payment Vehicles: Documentation of transfers via mobile payment apps (e.g., K+, SCB) and escrow accounts.
Transaction Metadata: Publicly shared receipts containing account numbers, partial names, and timestamps.
Logistical and Physical Interdiction Signals
Digital evidence must be linked to physical movement. Key indicators of transnational movement include:
Shipment Methods: Use of on-demand courier apps, public bus systems for regional smuggling, and "self-delivery" services.
Transnational Packaging: Identifying unique concealment methods and packaging labels in user photos to determine the point of origin and transit routes.
Documentation Signals: Sellers explicitly offering "no papers" for a higher price, confirming the illicit nature of the cross-border movement.
5. International Coordination and Regulatory Leverage
IWT is "structurally transnational"—sourced, sold, and marketed across different jurisdictions. National enforcement must be bolstered by international regulatory pressure.
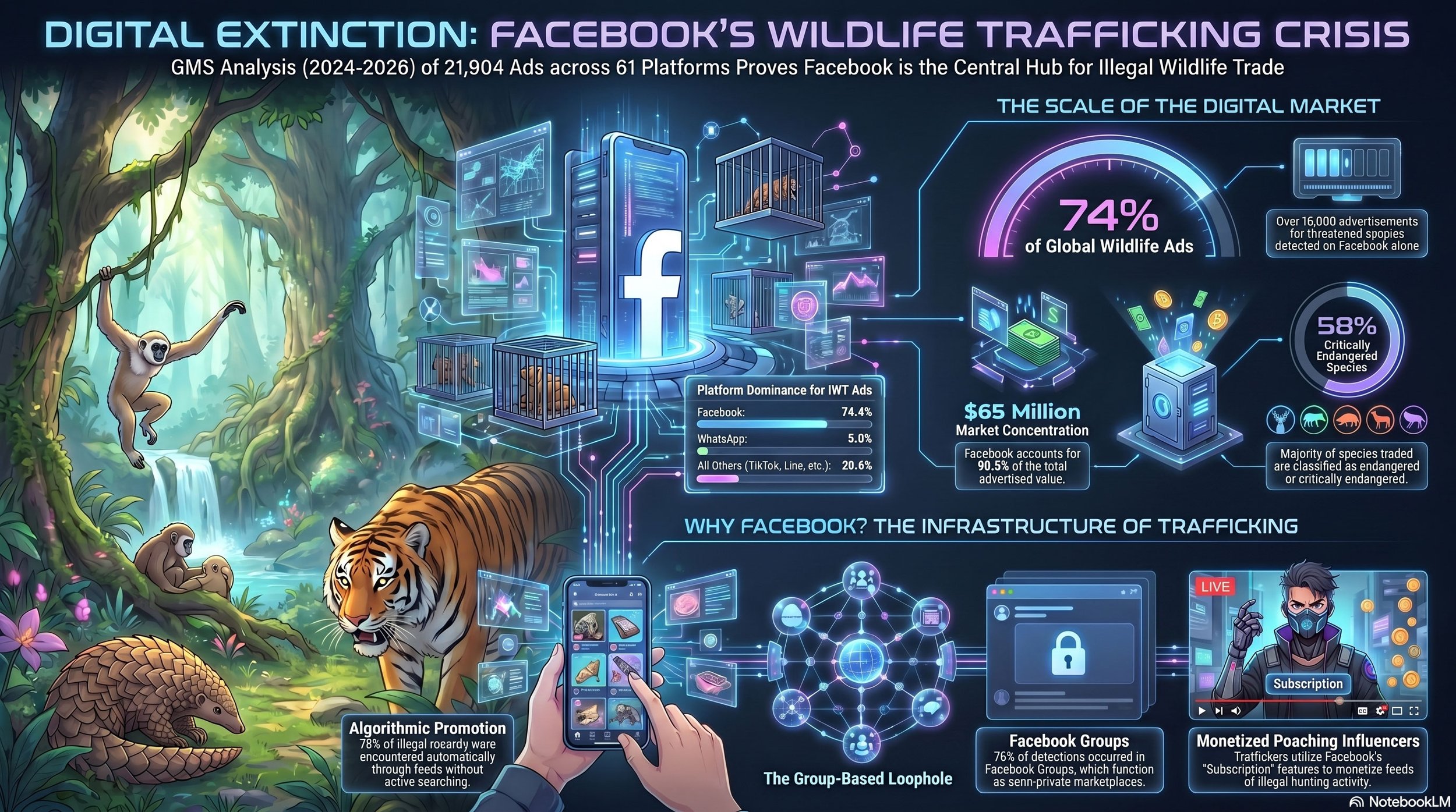
Legal Nuance and Enforcement Authority
Section 230 (US): While this provides broad civil immunity, it does not protect platforms from federal criminal law. Law enforcement must leverage this exception to compel data sharing and cooperation from US-based platforms.
EU Digital Services Act (DSA): This framework establishes "Enforceable Duties" of care. Regulatory bodies can use these to mandate risk mitigation plans and transparency regarding recommendation algorithms that amplify IWT.
Strategic Recommendations for Coordination
Mandatory Multilingual Detection: Demand that platforms deploy multimodal systems capable of identifying both code words (e.g., "re-homing fee") and product imagery across all 21 monitored dialects.
Trusted Flagger Pathways: Establish dedicated, rapid-response reporting windows for expert law enforcement analysts to ensure immediate takedown of high-priority criminal groups.
Algorithmic Audits: Require independent scrutiny of recommendation engines to ensure they do not function as a marketing arm for traffickers.
Monetization Oversight: Force platforms to revoke and investigate any accounts receiving "Subscription" or "Creator" funds that are linked to poaching and IWT display.
This protocol transforms platform design failures into a coordinated enforcement opportunity, utilizing the platform’s own architecture to map, track, and disrupt the criminal networks driving the sixth mass extinction.
Source: https://globalinitiative.net/wp-content/uploads/2026/04/Russell-J-Gray-Simone-Haysom-Wildlife-has-a-Facebook-problem-GI-TOC-April-2026.pdf